
You're now following
Error following user.
This user does not allow users to follow them.
You are already following this user.
Your membership plan only allows 0 follows. Upgrade here.
Successfully unfollowed
Error unfollowing user.
You have successfully recommended
Error recommending user.
Something went wrong. Please refresh the page and try again.
Email successfully verified.

bucha, ukraine
It's currently 6:08 AM here
Joined September 28, 2018
0 Recommendations
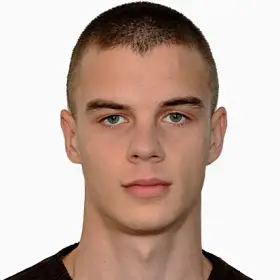
Vladislav K.
@workvl3
0.0
0.0
100%
100%

bucha, ukraine
N/A
Jobs Completed
N/A
On Budget
N/A
On Time
N/A
Repeat Hire Rate
Audio Producer & Sound Engineering
Contact Vladislav K. about your job
Log in to discuss any details over chat.
Portfolio
Portfolio
Beats & instrumentals
Beats & instrumentals
Beats & instrumentals
Sounds for films
Sounds for films
Sounds for films
Mastering sound
Beats & instrumentals
Beats & instrumentals
Beats & instrumentals
Sounds for films
Sounds for films
Sounds for films
Mastering sound
Reviews
Changes saved
No reviews to see here!
Experience
Bass pack
Feb 2018 - Mar 2018 (1 month, 1 day)
Bass sample pack (100 audio loops + 20 one shots)
Contact Vladislav K. about your job
Log in to discuss any details over chat.
Verifications
Invite sent successfully!
Thanks! We’ve emailed you a link to claim your free credit.
Something went wrong while sending your email. Please try again.
Loading preview
Permission granted for Geolocation.
Your login session has expired and you have been logged out. Please log in again.